
Year: 2016
Network Attached GPIO with HP Jetdirect
The goal of this is to create some network attached GPIO with some of the HP Jetdirects in my junk box. Here are some of the web sites used to figure this out:
- https://forum.sparkfun.com/viewtopic.php?t=12563
- https://blog.rhysgoodwin.com/hardware/print-server-power-control-hack/
- http://www.linato.net/jetdirect/
As far as hardware the project was started with a Jetdirect 300x this was replaced with a 170x. The 300x has 10/100 base t which is why it was initially chosen. This was later replaced with the 170x which is only 10 base t. If you are looking to buy hardware, shoot for the 170x. The 300x, at least the one tested, does not appear to be as stable as the 170x.
The Jetdirects did not come with a power supply. The power connector was a somewhat weird diameter. Sourcing the power supply on Ebay proved more time consuming and expensive than desired. The search did lead to this listing which is hilarious. Just picture a person driving with a wired network and a printer in their car. No one probably ever buys this…
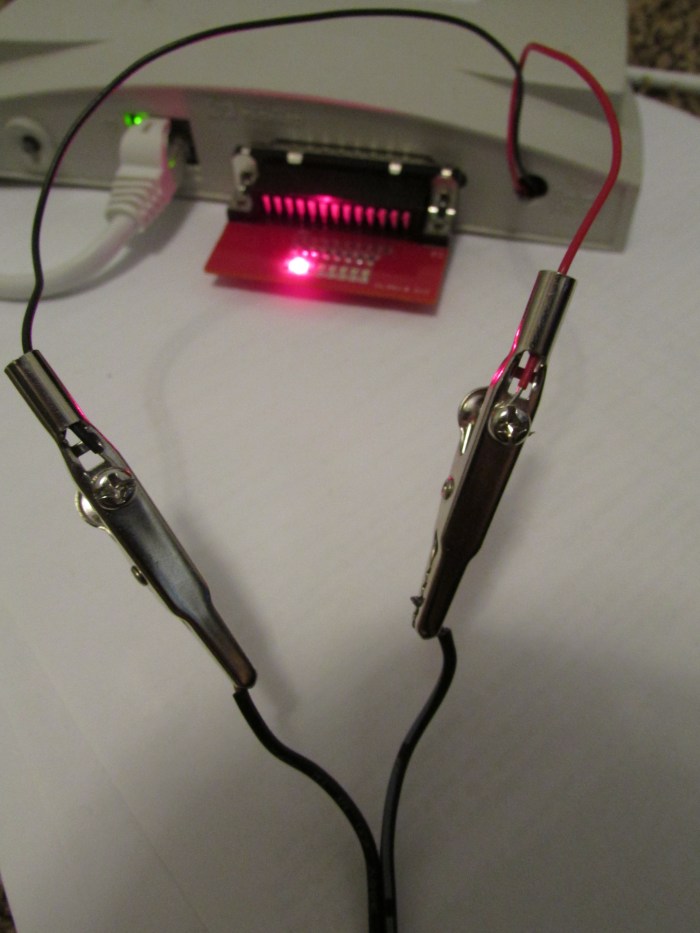
The easiest solution for this was to pop open the case and solder some wires to the power connectors. That was also a problem since HP was nice enough to use some super tiny Torx security bits. A quick trip to the hardware store and the screws were no match for my new set of security screwdriver bits.
These wires were then attached to a surplus 12v wall wart.
For testing a PCB was created and the design was sent to https://macrofab.com/.

The original PCB did not have the connection on the DB25 connector between pins 1, 10, 13 and 15. This was added later on with some red 30 awg wire wrap wire.
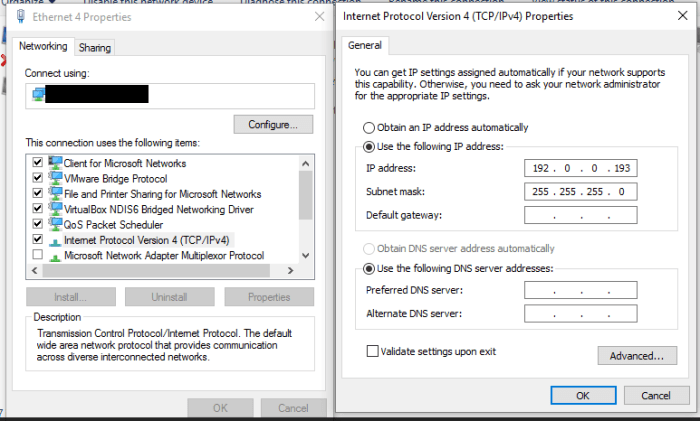
The first problem that was encountered was finding the Jetdirect’s IP address. Usually this would be a simple task. All that would be required is holding down a button on startup and the jet direct would print out a configuration page that lists its IP address. This would be easy other than the fact that I no longer own a printer with a parallel port interface. The device is supposed to have a default IP of 192.0.0.192 so that was tried first. After some reading it appears that if the device is power cycled while holding the
“test”button and releasing after 5 seconds it will go into reset and have factory defaults. After this was accomplished it was possible to ping, telnet and connect to the device using a web browser.
The telnet interface looked somewhat primitive so I opted for the web interface. The web interface failed to load in chrome so IE was tried. IE gave this lovely error:

After updating Java and adding the IP to the trusted sites in the java control panel, the web interface still did not work.

After some reading this is due to stricter security in the newer versions of Java. The work around for this was to use the telnet interface.
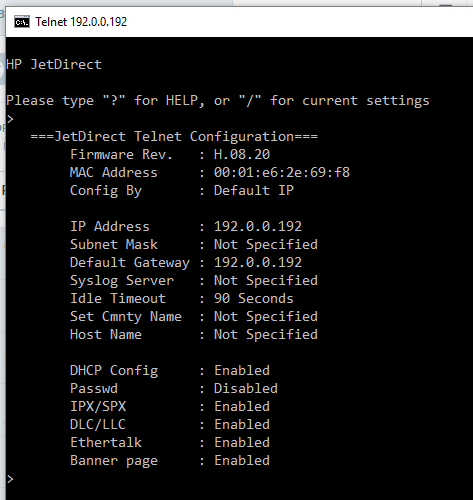
The jet direct’s default IP address of 192.0.0.192 was not convenient so it was changed to be in the 192.168.1.xxx range. This was done by issuing the command ip: 192.168.1.170 (or whatever IP you want) hitting enter then typing quit. After that wait one minute and power cycle the Jetdirect. The Jetdirect should now show up hopefully at the new IP. One other setting also needs to be set to gain control of the Jetdirect’s parallel port. The “set cmnty name” setting also needs to be set. This can be done by sending set-cmnty-name: private then typing quit.
One more thing needs to be done to trick the Jetdirect into thinking it has a printer attached. This is setting the npPortCentronicsHandshaking value in the jet direct. This was done with SNMPGetSet available here: http://www.fileguru.com/SNMPGetSet/download. The register is set by putting the value of 1.3.6.1.4.1.11.2.4.3.13.4.0 into the OID box at the bottom of the form. Once that is done hit the SNMPGet button. The returned value should be 3.

To set the value change the value in the box to 2. After changing the value of 2 make sure that you set the value type to ANS1_INT. Then press the SNMPSet Button. If you do not change the value type the setting will not save. You can confirm the setting was saved by pressing the SNMPGet button again.

If everything is working correctly the Jetdirect should now be able to be controlled. To verify everything is working correctly first check to see if the Jetdirect will open port 9100. This can be done from a Unix shell with netcat. Command nc -vz 192.168.1.170 9100 you should see [tcp/*] succeeded! if everything is working. If that does not work try port 23. If you can connect on port 23 but not on 9100 the Jetdirect does not think a printer is connected. Check your wiring especially on pins 1, 10, 13 and 15.
If everything works the fun begins. A printf "\xFF" | nc 192.168.1.170 9100 should turn on all the leds.
A sample program was constructed in C# to simulate the Knight Rider dash or a Cylon.
Here is the code: https://github.com/mdunakin/JetDirectDemo
Here is a video of the code running:
Network Caller ID (NCID) Install On Raspberry PI
This guide will walk through how to install network caller ID (NCID) on a headless raspberry pi. The primary goal of this is to create a blacklist to prevent unwanted spam telephone calls.
Hardware needed:
- Raspberry Pi, a model b was used but any should work
- SD Card, any larger than 4gb should work
- 5V power supply. The modem appears to take a large amount of current. The first 1 amp power supply was unstable so it was replaced with a 2 amp version
- Modem, a Zoom 56K USB Modem Model 3095 was used. This was sourced from Ebay.
- Phone cord
- A splitter. http://amzn.to/2fyT9hP to put the modem in parallel to the phone
How to install NCID:
- Grab an image of the Rasbian operating system from https://www.raspberrypi.org/downloads/ and install it to an SD card using this guide https://www.raspberrypi.org/documentation/installation/installing-images/
- SSH into the PI using putty http://www.putty.org/ User Name
piPasswordraspberry - Grab a copy of the NCID source code from here https://sourceforge.net/projects/ncid/files/latest/download using wget. Sourceforge can be a little strange so you may have to poke around to find the direct link
- Un-tar the archive using
tar -zxvf ncid-X.XX.X-src.tar.gz(replace the X.XX.X with version number) - Run
sudo-apt get updatethen grab a copy ofsudo apt-get install libpcap0.8* - Navigate to the folder with the build scripts and run
sudo make ubuntu-install - Open the config file with
sudo nano /etc/ncid/ncidd.conf - Make the following changes to the configuration file:
set ignore1 = 1# Make sure your modem is located here
set hangup = 1
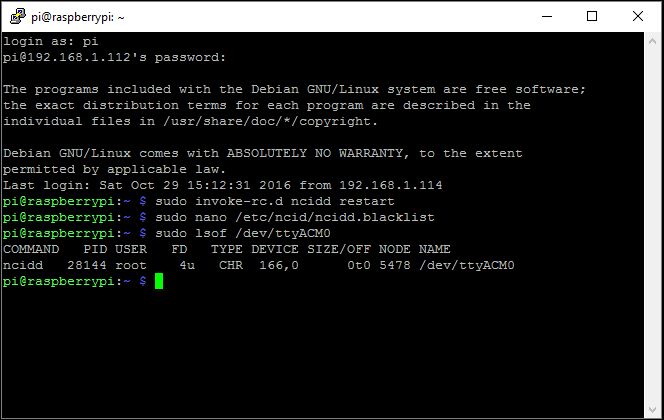
set ttyport = /dev/ttyACM0
set lockfile = /var/lock/LCK..ttyACM0 - open
nano /etc/ncid/ncidd.alias - Comment out this line with a “#”
#alias LINE - = POTS - Make the NCID daemon automatically start up
sudo update-rc.d ncidd defaults - The blacklist is located here and should be edited
/etc/ncid/ncidd.blacklist - Finally run
sudo invoke-rc.d ncidd restartto get the service running. This also appears to need to be run after editing the blacklist.
Notes:
- If the services is not working these links were useful during troubleshooting:
- This may or may not work outside the United States
- Commercial products exist that have similar functionality for around the same price http://amzn.to/2gFDrgP
- The caller ID will hang up after the first ring so not totally silent.
- Websites that spoof telephone numbers and caller IDs are available for testing.
- Since this is running headless the GPU memory can be decreased.
Deep Water Culture Hydroponic System
This is a short write up of the deep water culture hydroponics system that was just constructed. The water is housed in a food safe bucket from the hardware store. Food safe was chosen due to the fact that chromium and other heavy metals can leach from non-food safe buckets. The bucket contains a EcoPlus 396 gallon per hour pump without any nozzle. The bucket also contains a Tetra Whisper Air Pump connected to a large air stones with tubing and a back-flow valve to prevent water from siphoning back into the pump if power is lost. The pump and fish tank air pump are used to oxygenate the water for the system and keep the water moving so that it will not get stagnant.
The top of the bucket was drilled out with a 2″ hole saw . The holes are filled with 2″ mesh net pots. These pots allow the plants roots to grow down into the constantly moving water. The pots are filled with clay pebble grow media. Before this media was used it was washed multiple times to remove any excess dirt from the media. Then it was placed in the bucket for a few days with the fish tank air pump to oxygenate the stones. This was a recommendation from multiple sources found online.
The light is just a standard led spotlight bulb wired to a light timer to give the plants a sense of day and night. The pump and air pump will be run continuously while the system is operational.
The final step was transplanting in some plants and fertilizing the plants. General Hydroponics MaxiGro fertilizer was chosen since it has a PH buffer in it . The PH buffer hopefully will prevent having to adjust the PH of the system over time.
Here are some photos of the system:



Rfcat on eZ430-Chronos Dongle with CC-Debug
Steps to get Rfcat working on a eZ430-Chronos Dongle.
If you are interested on what Rfcat is watch this video https://youtu.be/ZWx8y5_J0Xo
Acquiring supplies
You will need 1 eZ430-Chronos kit (more specifically the PCB shown in the green box below)

Note: this will only work on older eZ430-Chronos dongles with the black PCB. The newer kits have a white PCB that contains a CC1101. To the best of my knowledge the Rfcat project only runs on the CC1111. The eZ430-Chronos kit used was purchased from TI on 08/2011 during a sale for $24.50 USD.
You will also need 1 CC-Debugger. They can be acquired from TI or in my case Ebay. Buying development tools from Ebay can be a gamble but the price was just too good for this CC-Debugger.

And here is the dongle and CC-Debugger:

Wiring:
Wiring the dongle is fairly straight forward. Since a bootloader will be installed it only really has to remain wired for a short period of time and does not need to be robust at all. Due to this some 30 awg solid core was used.

A diagram of how to wire the part can be found on page 47 of this pdf http://www.ti.com/lit/ug/slau292g/slau292g.pdf.
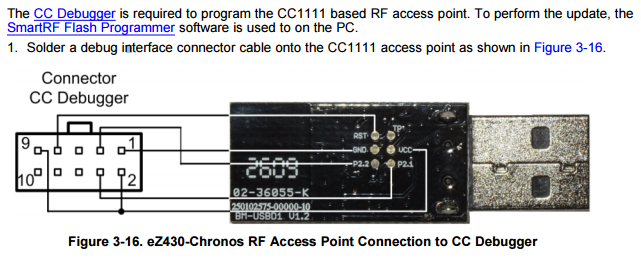
Note: the connector is wired as it would be looking into the CC-Debugger. If you are unsure of the connector orientation find a CC debugger pin-out and look at pins 1 and 9 (vcc and gnd) with a DMM.
Updating the CC Debugger
The easiest way to update the CC-Debugger to the latest firmware appears to be getting a copy of Smart RF Studio http://www.ti.com/tool/smartrftm-studio. Run the software with the CC-Debugger connected and you will be able to flash the CC-Debugger with the latest firmware.
Flashing the Chronos Dongle
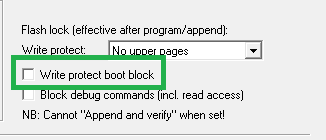
Flashing the chronos dongle was done with SmartRF Flash Programmer (Version 1) http://www.ti.com/tool/flash-programmer. Version 2 was avoided since it did not have an apparent way to write protect the bootloader.
The hex files for Rfcat can be found here: https://bitbucket.org/atlas0fd00m/rfcat/downloads
The bootloader (RfCatChronosCCBootloader-150225.hex) was written first:

Then the actual code was written (RfCatChronos-150225.hex) Make sure that the Write protect boot block check box is checked for this step.
If you have done everything correctly you now should have an Rfcat dongle.
Using the Rfcat dongle
An old netbook was used to test the dongle. It was re-formatted and 32 bit Ubuntu 14.04.4 LTS was loaded on to it http://releases.ubuntu.com/14.04/.
After setting up the OS python-usb and libusb were acquired.
After that the rfcat tarball was unziped and sudo python setup.py install was run to install rfcat.
A udev rule was added for the dongle but it ended up not working so it will not be documented. The tool can be run without the udev rule by issuing sudo rfcat -r

success!!
Poutine with homemade gravy and cheese curds

Making good poutine starts with high quality fries. The fries used for this are Heston Blumenthal’s (Link to fries). These are hands down the best fries ever. They are so crispy that the fried coating shatters when you bite into them. The fries stand up well to the gravy. Making these takes quite a long time with multiple frying and cooling steps. The multiple steps in the process are time consuming but there is enough downtime to make the gravy and cheese curds. The cheese curd recipe is from Home Cheese Making by Ricki Carroll. The curds were super squeaky when bitten into and turned out well. The gravy was made by making a rue then incorporating some home made beef stock. The dish was topped with this gravy and some freshly chopped parsley.
Wall Mounting TV
This is a post discussing wall mounting my TV. Here is the before photo:

Behind the left speaker is a computer that is connected to the TV. The white cabinet is hiding a router and cable modem. The house was wired with a cat 5 and coax run near the TV. After some searching an adapter was found that allows for HDMI to be run over CAT-5 (J-Tech Digital JTDHDEX-1 HDMI over single CAT 5E,6,7). With some re-wiring the Modem, computer and router were able to be relocated to the basement. The TV was mounted using a Cheetah Mounts APTMM2B TV Wall Mount. The computer was using a Logitech Keyboard K400 keyboard. This worked fine with the computer close to the TV. Once the computer was moved to the basement the keyboard was not as responsive as hoped. This was fixed by using a 50 foot active USB extender to move the USB adapter closer to the TV. Overall the install turned out clean with no visible cables:

Pantry Box Holder
This was project was done since no commercial product could be found. This was originally done with a wine box turned on its side with the lid removed. The box was getting a little worn out so a replacement was made. The replacement consists of 4″ square fence post cut to 12″ lengths. The 12″ lengths were attached together with construction adhesive.
Before:

After:

Lobster Ravioli
This was a fairly time consuming dish to prepare. This dish is lobster ravioli with homemade pasta in a brown butter sauce.
Steps:
- cook 2 lobsters in a large pot and clean off meat.

- While cooking lobster also roast garlic in oven. Zest and juice a lemon and chop some parsley.
-
Then mix the filling consisting of the lobster meat, lemon, parsley and ricotta cheese.

- Then make fresh pasta dough. Sheet the pasta cut it out and form the ravioli. While this is being done also brown some butter in a pan.
-
Mix heavy cream with the browned butter. At the same time boil the ravioli.

- Finally mix sauce and pasta and serve:








